Definitely not for an environment that boasts TBs of data that should be backed up the most efficient way. This solution is best suitable for environments where backups sizes are not exceeding couple of TBs in size as the BitLocker encryption will slow down the entire process by encrypting each new file during the initial copying. Once the first sync is over, consecutive synching should be far faster as only new and modified files will be copied & encrypted to the destination volume.
Further, the performance of the entire process depends upon the hardware resources available also. We deployed this solution for one of our businesses that has approximately 500GB total size, consist of hundreds of thousands of small files. The first robocopy run on each external disk over USB 3.0 took approximately 10-12 hours and the consecutive runs completed within 20-22 minutes. We used Tandberg RDX Quickstor External solution for this purpose. This time could be brought down to couple of hours if both source and destination volumes are based on SSD.
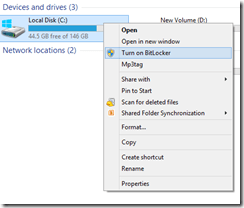
The solution approach was like this. All RDX tapes for 6 days per week were formatted as NTFS volumes, enabled BitLocker on them immediately after formatting.
The same machine Powershell was configured to run remote signed scripts. Powershell sample as below.
PS C:\Users\rajesh> Get-ExecutionPolicy
RemoteSigned
PS C:\Users\rajesh> $secretPW = "MySecretPassword123@" | ConvertTo-SecureString -AsPlainText -Force
PS C:\Users\rajesh> $secretPW | Export-Clixml -Path C:\Scripts\default.xml
PS C:\Users\rajesh> $MySecret = Import-Clixml -Path C:\Scripts\default.xml
PS C:\Users\rajesh> echo $MySecret
System.Security.SecureString
PS C:\Users\rajesh> Unlock-Bitlocker F: -Password $MySecretInterested about what happens when your password is converted to Secure String? Check the image below. That’s how a secure string looks & someone who has access to your computer/server could still be able to convert it to plain text and get your password. Hence, this is not a 100% fail safe solution, however it could be pretty effective against robots/malicious codes.

The above exercises were to confirm everything is in place and working properly before developing the script that will be used for regular backups. Name it anything and refer it inside the scheduled job.
#DailyBackup.ps1
#Author: Rajesh Thampi
#Date: 14.10.2024
#Read the BitLocker password from the xml file
$Secret = Import-Clixml -Path C:\Scripts\default.xml
#Unlock the volume that is BitLocer protected.
Unlock-Bitlocker F: -Password $Secret
#Setup source and destination paths.
$source='D:\Some_Folder'
$destination='F:'
#Start robocopy. Use /ZB switches to avoid recyclebin related issues.
Robocopy.exe $source $destination /E /DCOPY:DAT /XO /ZB
#After the copying, lock the drive immediately.
manage-bde -lock F: -ForceDismount
By the way, RDX hardware is not cheap. Hence you should consider alternative mediums. The advantage of a BitLocker protected volume is, even during a ransomware attack these volumes could be completely immune, unless the volume is open for backups during the attack. Well, you never know.
References
- https://www.ajni.it/2020/05/powershell-encrypt-and-store-your-credentials-securely/
- https://superuser.com/questions/1836226/powershell-how-to-unlock-bitlocker-encrypted-drive-simple-way
- https://winaero.com/how-to-lock-bitlocker-encrypted-drive-in-windows-10/
- https://stackoverflow.com/questions/68947647/create-secretstore-vault-without-a-password